Listen to the article
Research has revealed that fake social media accounts could be responsible for serious security breaches, according to a groundbreaking study led by the University of Portsmouth. The findings underscore an urgent need for enhanced security training and more stringent controls over fraudulent profiles across digital platforms.
The comprehensive investigation demonstrates how seemingly innocuous fake accounts can serve as gateways for sophisticated cyber attacks, creating vulnerabilities within organizations that traditional security systems may fail to detect. Researchers found that social engineering techniques deployed through these fake profiles have become increasingly sophisticated, enabling attackers to bypass conventional security protocols.
Dr. Emma Harrison, lead researcher and cybersecurity expert at the University of Portsmouth, explained the gravity of the situation. “What makes these attacks particularly dangerous is their psychological component. Unlike brute force attacks on networks, these methods exploit human trust and professional courtesies that are common in workplace cultures,” she said.
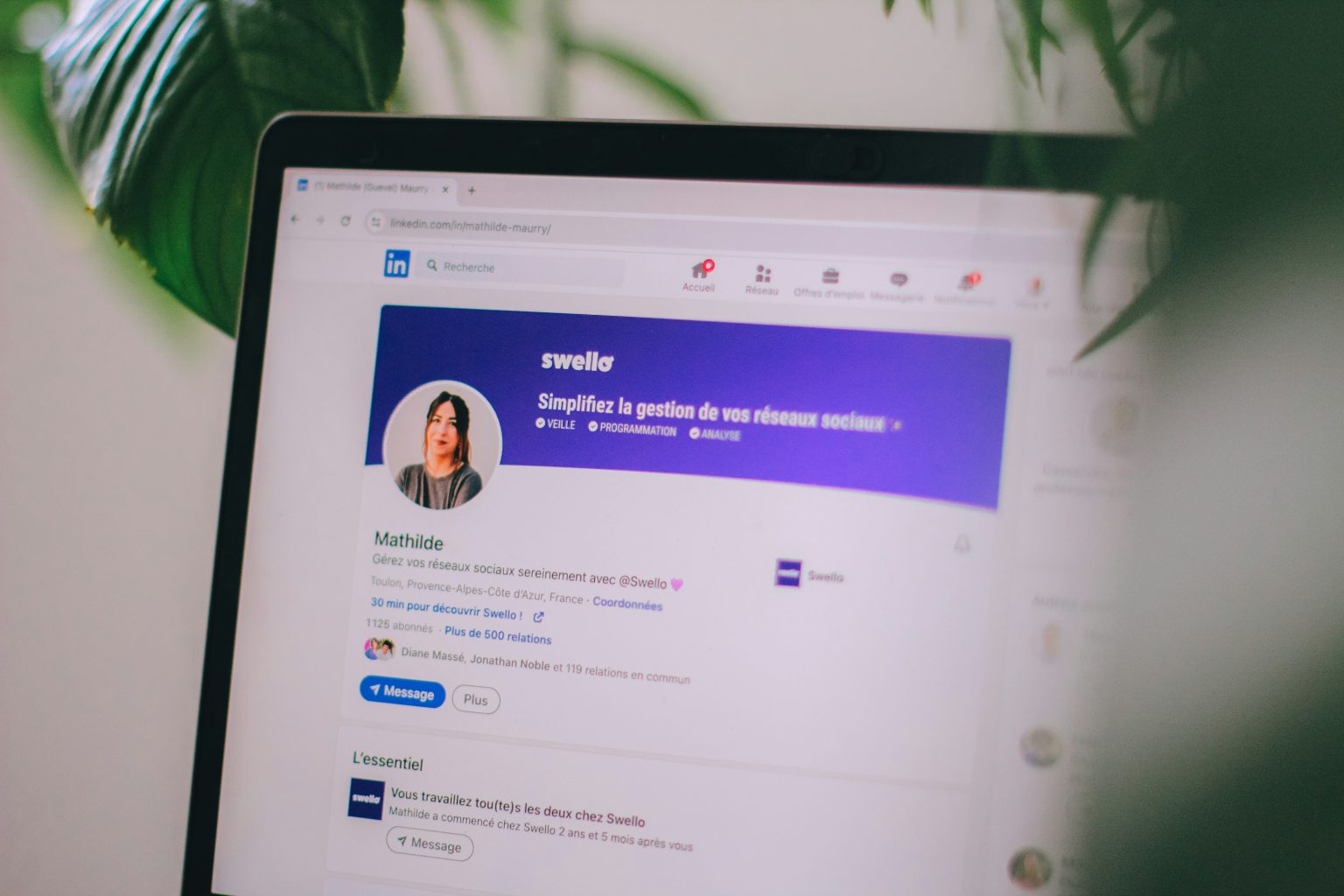
The study revealed that LinkedIn has become a primary target for such attacks, with researchers identifying a 43% increase in sophisticated fake profiles targeting professionals in key industries over the past two years. These accounts typically mimic legitimate professionals, often claiming to be recruiters, industry consultants, or potential business partners.
According to the research team, these fake profiles frequently engage in a months-long “grooming” process before attempting to extract sensitive information or gain access to secure systems. This patience makes them particularly difficult to identify through automated detection systems.
“The attackers are playing the long game,” noted co-author Dr. James Wilson from the university’s Center for Cybersecurity. “They invest significant time building relationships and credibility before making any moves that might trigger suspicion. By that point, they’ve often already gained considerable trust from their targets.”
The research documented several case studies where employees at financial institutions and defense contractors unwittingly provided access to sensitive information after prolonged interactions with what appeared to be industry colleagues. In one instance, a senior executive at a major European financial firm shared internal documents with a fake account posing as a regulatory consultant, resulting in a significant data breach.
Industry experts have responded to the findings with concern. “This research confirms what many security professionals have suspected but couldn’t quantify,” said Catherine Davis, Chief Information Security Officer at a leading UK financial services company not involved in the study. “Social media has created an entirely new attack vector that many organizations haven’t properly addressed in their security frameworks.”
The researchers recommend several immediate actions for organizations to mitigate these risks. These include implementing specialized training programs focused on identifying suspicious social media contacts, establishing clear protocols for information sharing with external parties, and developing verification systems for new professional contacts.
Major social media platforms have also been urged to enhance their detection and removal processes for fake accounts. While companies like LinkedIn have introduced various authentication features, the study suggests these measures haven’t kept pace with increasingly sophisticated impersonation techniques.
The implications extend beyond corporate security. The study identifies potential national security concerns, with evidence suggesting state-sponsored actors are utilizing similar techniques to target governmental and defense institutions.
“What begins as a seemingly innocent connection request can ultimately compromise systems containing highly sensitive information,” warned Professor Alan Thompson, cybersecurity advisor to several government agencies. “Organizations must recognize that their security perimeter now extends to their employees’ social media activities.”
The University of Portsmouth research team plans to expand their investigation to examine effective countermeasures and develop training modules that can be implemented across various sectors. They have called for increased collaboration between academia, industry, and social media companies to address what they describe as “one of the most overlooked security vulnerabilities in modern digital infrastructure.”
As organizations increasingly rely on digital networks and remote work arrangements, the findings underscore the critical importance of human factors in cybersecurity frameworks and the need for more sophisticated approaches to combating social engineering attacks.
Verify This Yourself
Use these professional tools to fact-check and investigate claims independently
Reverse Image Search
Check if this image has been used elsewhere or in different contexts
Ask Our AI About This Claim
Get instant answers with web-powered AI analysis
Related Fact-Checks
See what other fact-checkers have said about similar claims
Want More Verification Tools?
Access our full suite of professional disinformation monitoring and investigation tools